Timeline

Finding Gaps in Timestamps
Sometimes knowing when something didn't happen can be just as valuable as knowing when it did. For reasons yet to be determined, my Salt Master server needs to be bounced occasionally. Not the whole server - just the salt-master service. I needed to find a good time to do this.
The Black Box on the Org Chart
There’s a particular kind of delusion that takes hold in tech booms. It starts with a true thing, wraps itself around a useful thing, and then inflates into a preposterous thing.
The Post-Language Future of AI Systems
There’s a persistent assumption baked into how we talk about AI: that language is fundamental. That intelligence expresses itself through something like English, or at least through structured programming languages we recognize. It’s a comforting idea. It’s also probably wrong.
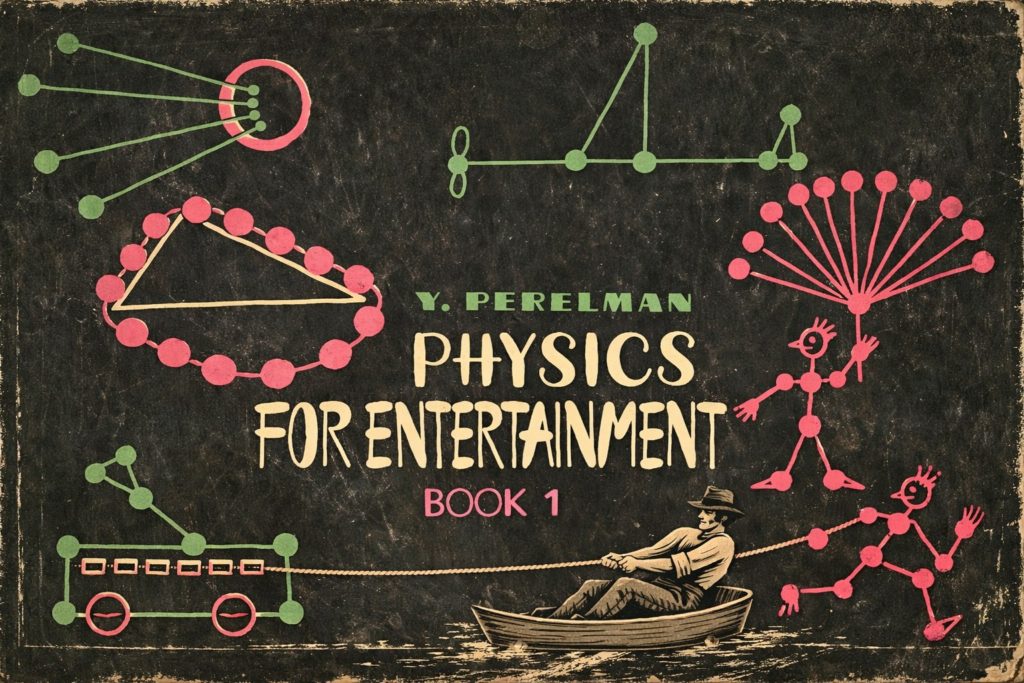
Outsmarted by a River, a Rope, and an Anchor
Before you entrust serious decisions to AI, consider that the most advanced systems routinely fail at school-level physics problems written over a century ago. Here's why, and what it reveals about how these systems actually "think."
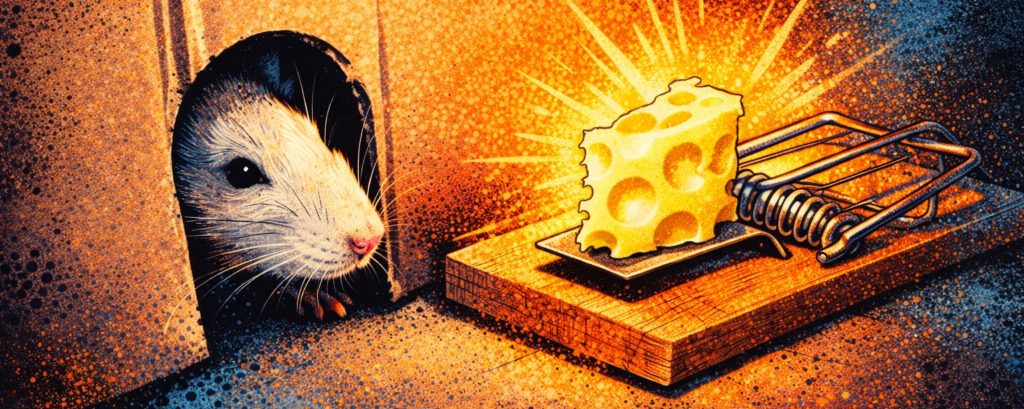
The AI Bubble Isn’t a Bubble. It’s a Trap.
Let’s dispense with the fantasy right away. Your $20-a-month ChatGPT subscription isn’t paying for anything remotely resembling the actual cost of running modern AI. It doesn’t cover the data centers, the power bills, the GPUs stacked like gold bars in climate-controlled bunkers. Not even close.
Coronavirus Stats in Bash
The result of my morbid fascination with the coronavirus situation is this quick bash script that parses Johns Hopkins University coronavirus data to generate a quick report for the current date for the specified countries.
Updating Lynis
Lynis is an excellent security audit tool for Linux and various Unix derivatives. I have a small wrapper script that runs Lynis via a cron job, does a selective diff with the previous run's output, and sends me an email.
Converting Geofency Data to Google Maps
Geofency is a time and location tracking app for iOS. I've been using it for many years to keep track of my whereabouts. At times, this information can come in quite handy.
Canyonlands National Park, Utah
In July, some friends and I went on an 8,000-mile overlanding trip to Colorado, Utah, Wyoming, and South Dakota. One of the first stops was Canyonlands National Park. Here are some photos from there and other nearby areas we visited on our second week of the adventure.
Reading Multi-Line Input in One Loop Iteration
Bash loops can read the input as words or lines, but what if you needed to accept multi-line input with a single loop iteration?
Yellowstone National Park, Wyoming
In July, some friends and I went on an 8,000-mile overlanding trip to Colorado, Utah, Wyoming, and South Dakota. One of the first stops was Yellowstone National Park. Here are some photos from there and other nearby areas we visited on our third week of the adventure.
Convert Code Snippets to PNG
On occasion I find myself struggling posting code on discussion forums that don't handle code formatting all that well. What would've helped is some quick and easy way to convert code to an image file with syntax highlighting. And so here it is.
Backup Options for Raspberry Pi
Just about every Raspberry Pi I used suffered the same fate: the micro SD card died. It is generally accepted that the expected lifespan of an SD card is around ten years of normal use.
Affordable Linux Server
A friend asked me what server I would recommend to run Linux. Yes, a very broad query. After a few followup questions we've determined the server will be used to run VMs, or Apache, or a database, or maybe a mail server, or FTP. Right...
Linux Blog Directory
A curated list of Linux and Unix blogs from around the world.
Backing Up WSL Images
Microsoft's WSL is interesting. I'd go as far as to say that I like it. The mistake here would be to forget that your Linux image is running under Windows, with everything this entails. Making a reliable backup of this thing proved harder than I expected.
Home-Brew Ransomware Defense
The first well-known case of ransomware was documented in 1989. The so-called AIDS Trojan was delivered on a floppy disc; encrypted data; demanded $189.00 (nearly four hundred bucks in today's money) as a "license fee." The trojan was quickly defused due to its reliance on weak symmetric cryptography. In contrast,…Read More
Validating HTTPS Cache Peers for Squid
I have a squid proxy server that uses a long list of authenticated cache peers in a round-robin configuration. The process looks something like this:
Fuzzy Search with Linux
This is a quick look at several handy utilities that will allow you to find, navigate, and edit directories and files easily. This overview includes such tools as fzf, rg, fd-find, bat, and the fzf.vim plugin for VIM.
Updating PHP 5.6w to 7.1u on CentOS 6.10
This is mostly just a note to self. As I mentioned previously (probably more than once), I very much dislike systemd and will stick with CentOS 6 for as long as possible. Having said that, WordPress dashboard has been nagging me about having to update PHP. So here we go.
Analyzing atop Logs with atopsar
I have discussed atop previously but concentrated primarily on how to run it and how to collect data. Now I'd like to spend some time talking about ways to analyze the data collected with atop.